The cyber risk facing the manufacturing sector is likely greater at this point than ever before. Cybercriminals have demonstrably pivoted towards targeting manufacturing sector companies, likely after recognizing the sensitivity of manufacturing towards extended outages. This observation has been confirmed by our analysis of ransomware activity in 2021 and 2022. There is also an ever-present threat from nation-state attackers, looking to access intellectual property held by manufacturing companies and exploit the relationship between vendors to move laterally. The following blog details why manufacturing is such an attractive target.
Why is manufacturing such an attractive target?
Since the turn of the industrial revolution, the global economy’s health has inherently been linked to manufacturing; innovation and financial growth can only be achieved with a consistent and robust manufacturing output. Productivity growth in other sectors of the economy is also a result of innovations in the manufacturing sector. For example, the food and beverages and farming sectors are inherently dependent on the continual output of chemicals, fertilizers, pesticides, and agricultural machinery.
One reason manufacturing could be identified as a sector to target is because of its inherent susceptibility to outages. Nowadays, the production of goods and products simply can’t happen without the consistency of IT processes; this has largely coincided with the adoption of digital transportation programs and smart technology that is designed to improve efficiency. However with these improvements come some risks; if the lever gets pulled and production can’t continue, manufacturing ceases to function. You could probably say that about a lot of sectors, but manufacturing, in particular, will significantly suffer from extended periods of downtime.
The manufacturing sector also contains partnerships with almost every other sector, including government, defense, healthcare, and technology. Those associations provided excellent opportunities for threat actors, such as the ability to access to intellectual property (IP) and to move laterally into other networks of interest. We’ve previously reported on the motivations of the Peoples Republic Of China (PRC) linked threat groups, who are mostly concerned with the mass exfiltration of sensitive data to support China’s technological and economic ambitions. This is also relevant to Russian state-sponsored groups, many of whom will likely be tasked with identifying and stealing IP following the fallout of Russia’s invasion of Ukraine; one example of this fallout is the lack of smart weaponry being used by Russia in the conflict, due to the impact of western sanctions on certain technological parts. If Russia can’t produce them on their own, and they can’t import them from the West, you can guarantee they’ll try and steal the IP for them.
It’s also possible that the manufacturing sector simply isn’t as resilient to cyber threats as others. This may be down to a lack of resources, a lack of understanding of the threats, or simply due to the nature of this business. This was emphasized by a recent report issued on cloud security which identified the scale of problems facing manufacturing companies when attempting to secure data.
Cloud security challenges facing manufacturing (Source: Netwrix)
While it’s only one example, my thoughts immediately went to the case of United Structures of America, a construction company that went under due to the impact caused by a ransomware attack. In the incident, the company couldn’t recover their files due to a lack of working backups (that hadn’t been tested), had no incident response or insurance, and were forced so were forced to pay the attacker’s demands. The company was then hit by ransomware again, and unfortunately was forced to cease operations as a result of the incident.
Ransomware poses the biggest cyber risk to manufacturing companies:
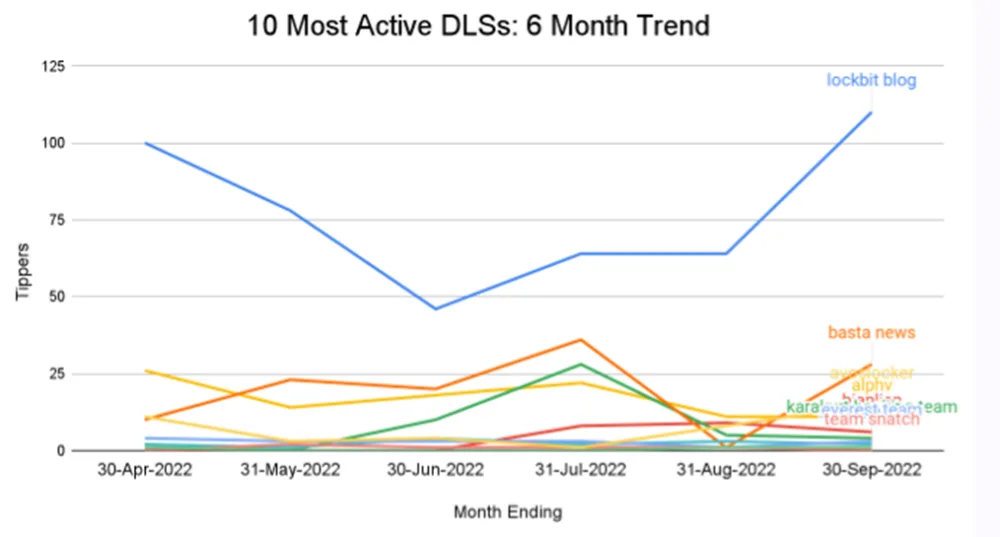
While we’re on the topic of ransomware, ReliaQuest’ analysis of ransomware activity, by tracking postings on individual ransomware group’s data leak sites, identified that manufacturing was the most commonly targeted sector in the last 6 months. This was also almost twice as large as the second most targeted sector. Similar results were also observed in 2021 and are likely to continue for the medium-term future (3-6 months). This can be seen in the graphic below, identifying the number of ransomware posts per sector for six months preceding 16 August 2022.
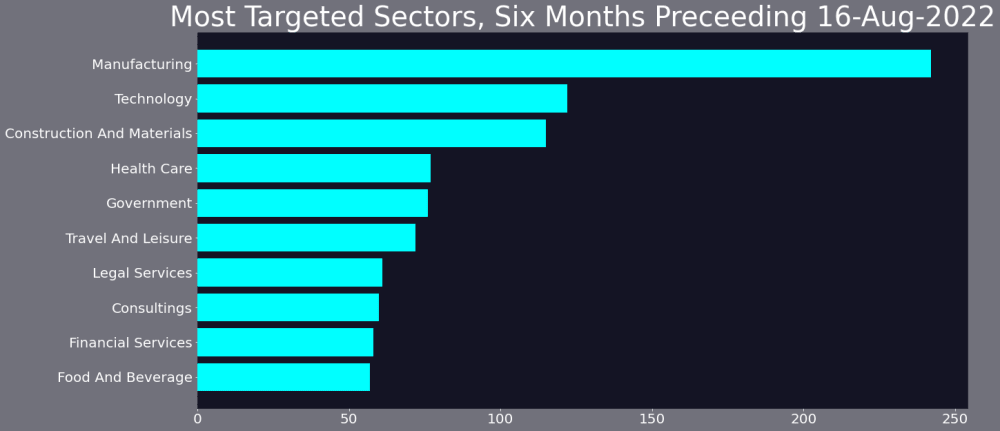
Ransomware tippers by sector: 16 Feb 2022 – 16 August 2022 (Source: ReliaQuest)
Without trying to teach everyone reading this to suck eggs, it’s almost certain that we’ll see similar or increased levels of activity from ransomware groups in the remainder of Q3 and Q4 2022. This will of course impact numerous sectors but in particular, those involved in manufacturing—largely for the reasons we’ve outlined above.
2022 has actually seen an overall decrease in the levels of ransomware activity overall, which is likely as a result of global issues and geopolitics; yes Ukraine and Russia, REvil arrests, we’re looking at you. If you’d like a more in-depth look at the ransomware landscape, including predictions on how the activity will accelerate in Q3 and Q4 2022, check out our recent quarterly blog.
Opening the door with account takeover
Our recent research report identified the significant risk associated with account takeover (ATO) and stolen credentials. The use of ATO permits a huge percentage of cybercrime, with over 50% of incidents reportedly resulting from the acquisition and exploitation of stolen credentials. This is a problem that has persisted for many years, despite the advancements of controls and the use of password managers, two-factor authentication, and improving password complexity requirements. This problem has coincided with a rise in initial access broker activity, who act as cybercriminal middlemen in establishing and selling exploited accesses into various networks, which of course, also go hand in hand with ransomware groups.
This is another cross-sector problem but one that is likely to be particularly prevalent in manufacturing. One of the reasons for this is the prevalence of companies being forced to adapt for remote workers, which has been prioritized following the COVID-19 pandemic and as a natural consequence of digitization. Pressure to move to remote work has resulted in an increased attack surface—which if coinciding with insufficient identity management—can present a significant risk; the example we provided earlier with United Structures of America, reportedly resulted from the compromise of an administrator’s privileged account, which had a particularly weak password.
Nation-state risks and supply chain compromise:
The manufacturing sector is also a high priority for nation-state-associated threat groups, who likely recognize the opportunities for lateral movement and supply chain compromise. There is also the possibility for retaliatory attacks to be conducted at manufacturing companies in retaliation for sanctions or other geopolitical events.
Nation-state attackers are by nature extremely sophisticated and operate with varying motivations. The impact that can be caused by such groups is, therefore, less predictable than cyber criminals; e.g. the goals of a PRC-related threat group may be to establish long-term persistence and exfiltrate intellectual property, while a Russian threat group may be more destructive. Of course with manufacturing, destructive attacks can have physical consequences, which is why it’s as important as ever to keep attackers off your network.
Improve your cyber resilience:
Cyber resilience refers to an organization’s ability to continuously deliver its intended outcome, despite the prevalence of cyber attacks. As we detailed above, manufacturing is arguably one of the most susceptible to extended outages, which when combined with an often insufficient cyber security program, can present serious problems. While there’s a lot that can be mentioned here, three tips on how to strengthen your resilience to these various attackers can be seen below.
Internet-facing remote services: Citrix, Virtual Private Network, Remote Desktop Protocol. None of these services should be unnecessarily exposed to the internet or be used with weak and default credentials. We talked about ATO earlier in this blog; this is one of the most common methods for stealing users’ accounts and using them to gain access to networks.
Identity and access management (IAM): IAM ensures that authorized people— and only them—have access to the technology resources they need to perform their job functions. Properly identifying, authenticating, and authorizing people and technology is key to ensuring that if a compromise does occur—either of an account or at an endpoint—the damages can be minimized.
Vulnerability management (VM): VM provides a way to reduce the network attack surface, the exploitability of critical assets, and the risk of business impact. We previously released a research paper on vulnerability intelligence, detailing the requirements for a risk-based approach to vulnerability management. Establish your assets, identify the vulnerabilities that affect them, and fix them in order of severity.
If you’re curious how intelligence can work for you, especially when it comes to your sector, assets, or digital footprint, you can take ReliaQuest GreyMatter DRP for a 7-day test drive and see what the bad guys are doing out there. If you have some particular needs or questions, chances are we understand your use case, so contact us for a demo of Searchlight.




