As I spent Wednesday night doom scrolling into the early hours of the morning, I felt pretty powerless as I watched the tragic Ukraine crisis unfold. On Thursday, I decided to put this blog together to help security leaders and practitioners prepare for potential Russian cyber threats that could impact their organizations. This thought process began with this Twitter thread which I consolidated into this blog. You can read our latest assessment “Russia Invades Ukraine: What Happens Next?” from February 24th for more details on our overall perspective.
This blog is going to take a similar approach to a blog I did just over two years ago when the United States assassinated Iranian General Qasem Soleimani: “Iranian Cyber Threats: Practical Advice For Security Professionals.” I want to avoid hyperbole, knee jerk reactions, and give you seven pragmatic recommendations that I hope make your lives a bit easier.
Before we start, I have to take a moment to recognize the absolute human tragedy that is underway; it is heartbreaking. It is also essential to put our cybersecurity jobs in the proper context. We are defending networks in cyberspace; meanwhile, there are men, women, and children hiding in Kyiv subways worried about their actual lives. I live here in North Texas, and I like the Dallas skyline right about now. The local community is rallying around the Ukranians that live here.

Credit: WFAA/Jon Goss
Take care of the team
You must prioritize the mental health and well-being of the team. Set up rotations for the team; have refreshed resources. Log4J just happened, and many organizations are dealing with the aftermath of that.
Deprioritize other work so you can adequately respond to this conflict. You can’t maintain your traditional operational tempo and production while adding the most significant European crisis since WW2 to the to-do list.
Track compensation time. If someone has to work over the weekend, make sure that the analyst gets that time off soon. This recovery time is critical if your organization’s cyber response becomes protracted. Treat this crisis as a marathon and not a sprint.
Finally, leaders must model self-care for their teams. You cannot be focused on the team and your responsibilities if you aren’t taking breaks to eat, work out, sleep; you set a terrible example for the team.
Know your threat model and where Russian actors rank
In response to Western actions, Russia isn’t going to target “all the things.” Not all organizations are on a targeted attack hit list back in Moscow. Your mileage may vary, but most defenders should be more concerned with commodity ransomware than Russian APTs. If you have business interests or business partners in Ukraine, your threat model changes. You do need to be flexible, actors objectives and operations change; a low risk threat yesterday could become the most important threat tomorrow.
Specific industries are more likely to be targeted by Russia. Watch the Western sanctions closely; Russia could choose tit for tat targeting and go after the equivalent of any Russian company or individual sanctioned. Banks and the energy sector are likely targets in this scenario.
After Wednesday’s Nord Stream 2 gas project announcement, Germany should be on high alert. Germany’s saving grace could be the unwillingness to kick Russia off the SWIFT network. Boris announced sanctions yesterday, and UK entities could be targeted as a result. The Biden administration announced additional limited sanctions as well.
As I said, everyone isn’t on the target list, but there could still be unintended victims of Russian targeting. Think Maersk in 2017 and the NotPetya attack that cost hundreds of millions of dollars. A wormable attack could impact almost everyone; once the genie is out of the bottle, you can’t put it back in.
One specific threat to watch out for is how Russian aligned extortion crews like Conti respond to the crisis. On 25 Feb 22, the Conti ransomware group announced their support for the Russian government, and claimed that any targeting of the Russian state in cyberattacks would result in Conti using “all possible resources to strike back at the critical infrastructure of an enemy.” Their statement represents the first major cybercriminal group to publicly back the Russian war effort and follows recent warnings from US officials, who emphasized that the risk from ransomware activity may escalate as sanctions impact Russia. Check out our “Ransomware Q4 Overview” blog for more details on Conti and overall extortion trends.
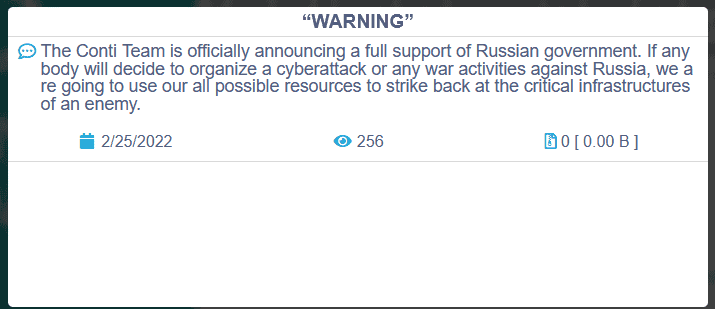
Conti News site
Communicate effectively up the chain of command
Everyone has been there; you receive an email or a Slack from the CISO or CEO asking about the latest threat de jour article making the morning headlines. I feel bad when I send these messages to our internal teams. Shame, shame, I know.
Now is the time to get ahead of the news cycle. You need to shape your leadership’s view of the Russian invasion and its meaning to your organization. Don’t let WSJ/Fox/FT/* drive the narrative. These headlines are a strategic opportunity to show the value of your threat intelligence team.
Take external reporting from a friendly neighborhood threat intelligence provider like ReliaQuest and enrich it with your internal context. What does this invasion mean to your firm, your staff, and your risks? Assess and explain the risks, the likelihood, impact, and your strategy going forward. This conversation should be a no FUD zone.
Establish a standard cadence for briefing updates. You are going to do X updates per week on these days. You will cover X topics. Get with the executives and see if they have questions they’d like answered. Develop intelligence requirements for both your questions and their questions and be ready to answer them on an ongoing basis. Get feedback from them after you deliver your first briefing.
Conduct tabletop exercises now
If Russian actors are in your threat model, and you haven’t already conducted tabletop exercises on DDoS & destructive wiper malware, I would schedule them ASAP. These are the most likely scenarios to play out. If you have completed a recent tabletop exercise, pull out the after-action review and refresh yourself. Hopefully, you have implemented some of the previous lessons learned.
Include senior leadership in your tabletop exercise. At ReliaQuest, we incorporate a tabletop exercise into a broader purple team exercise. We get two for the price of one; executives role play the same scenario that the technical teams put into action. We come up with improvements from the hands on keyboard team members all the way up to our CEO, Alastair Paterson.
What I love about tabletops is they don’t cost you much. In fact, tabletop exercises will help you make better investments in people, processes, & technology. Tabletop exercises mitigate the “expense in-depth” purchase mentality. Buy the right things, not the new shiny things. I guarantee that if you conduct an exercise next week, you will develop numerous process improvements you can immediately implement to improve your resilience to Russian cyber threats.
CISA provides excellent templates that you can build upon: CISA Tabletop Exercise Packages (CTEPs). You could customize the ransomware and ICS scenarios to help plan for cyber threats associated with Russian actors.
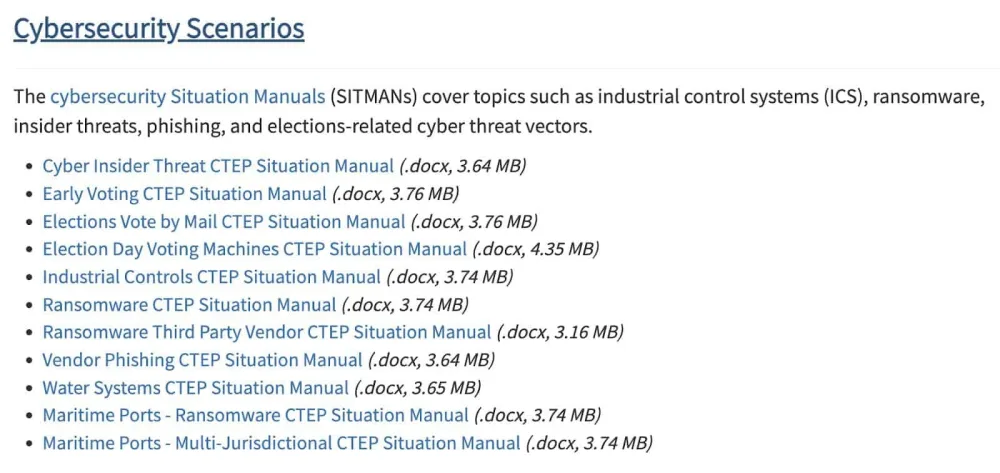
CISA tabletop exercise packages
Prepare your DDoS mitigation strategy
Russia has employed DDoS attacks for many years; see Estonia in 2007. I’m not going to argue whether DDoS should be called an attack or not; I’m just going to suggest options. If a DDoS attack from Russian actor is in your threat model, then:
Assess your current mitigation capabilities. Do you have on-premises gear, upstream ISP protection, or a DDoS mitigation service (e.g.,” Cloudflare, Akamai, Radware)? Understand the solution and how much bandwidth protection it offers. I’ve not been able to find numbers on the size of this week’s Ukrainian DDoS attacks, but it was reported to be substantial. https://www.cyberscoop.com/ukraine-government-networks-ddos-disruption-russia-invasion/
If you don’t have a solution in place, now is the time to reach out and start talking to providers. One does not simply find a DDoS mitigation service in the midst of a DDoS attack. Define your requirements and evaluate vendors before an attack occurs.
Assess the likelihood of an attack, and make a risk-based decision on whether to implement a DDoS mitigation solution. One positive for CISOs justifying the business case; is there aren’t many security controls that you can easily quantify the value of the protection. Calculate the downtime or lost revenue of an e-commerce website and compare that against the cost of the mitigation.
Prepare your destructive wiper malware strategy
Unlike ransomware where you could conceivably recover your data, destructive malware wipers go “scorched earth” and take out your infrastructure. SentinelLabs researcher Juan Andrés (aka JAGS) wrote up an excellent assessment of HermeticWiper, which was deployed against Ukraine this week. You can use intelligence produced from security researchers to guide your wiper malware strategy.
Several threat actors have leveraged destructive malware in the past, and Sandworm is the most relevant to the current conflict. Sandworm made the headlines this week with an alert announcing Cyclops Blink has replaced the VPNFilter malware.
The MITRE ATT&CK framework has profiles of prominent actors who have leveraged wipers. You can use these profiles to shore up your defenses to this type of attack: Sandworm, Lazarus Group, and APT33. You should familiarize yourself with Sandworm in particular and be on the hunt for any new intelligence related to its activities.
In January, in response to WhisperGate, which targeted Ukraine, CISA provided guidance “Implement Cybersecurity Measures Now to Protect Against Potential Critical Threats” that is worth checking out. It can help you protect against, detect and respond to wiper malware.
Leverage threat intelligence
Threat intelligence can play a decisive role in navigating the threat landscape and what the Russian invasion of Ukraine means to you and the rest of the world.
Threat intelligence starts at home; before you look for any free or commercial third-party intelligence, you should begin with your data and telemetry. Your internal data is unique and relevant to you; I know it sounds obvious, but often, people want to buy all the threat feeds without focusing internally. You should develop intelligence requirements to help understand the Russian threat to your organization. Last year, we did a blog to help you with this: “Let’s Talk About Intel Requirements.” Once you have defined your requirements, you can develop a collection plan that uses internal and external sources to answer the questions.
Governments are putting out helpful information about the current Russian threats and threats in general. The United States’ Cybersecurity and Infrastructure Security Agency has made recommendations through the Shields Up initiative. You can follow CISA on Twitter here, and CISA puts out regular threat updates and advice you should read. The United Kingdom’s National Cyber Security Centre (NCSC) has guidance on how to bolster defenses here. You can follow the NCSC on Twitter here.
Establish and maintain relationships with your peers/competitors for industry-specific threat intelligence. There are private trust groups where teams collaborate for the greater good. In the United States, the Information Sharing and Analysis Centers (ISACs) and the Information Sharing and Analysis Organizations (ISAOs) for your sector are good places to go. The FS-ISAC and the various energy-related ISACs would be good to be active in. From a commercial threat intelligence provider perspective, I’d like to highlight the good folks at Dragos who focus on OT/ICS/IIoT cybersecurity and threat intelligence. CEO Robert M. Lee has even offered up a free community version of their capabilities which is great.

Don’t focus on the threat du jour, play the long game
The more you prepare in advance, the better off you will be. The best time to prepare for a cyber threat was years ago, but better late than never. Building a resilient cybersecurity program takes time; there is no easy button to protect your organization. Don’t hyper focus on Russian cyber threats; instead build a program to protect against most threats.





