In the first quarter of 2022, several high-severity vulnerabilities were targeted by threat actors to facilitate malicious campaigns. The first quarter of 2022 has continued with the tempo set at the end of 2021 – notably, threat actors continued to target the Log4Shell vulnerability that was discovered in the fourth quarter of 2021.
The fallout for many of the incidents observed is yet to be determined, with ongoing investigations likely to uncover further details surrounding the source and motivations of the responsible attackers. In this blog, we look at the top five events and trends that emerged in the first quarter of 2022.
Remote Code Execution (RCE) vulnerabilities steal the spotlight
Remote code execution (RCE) vulnerabilities represent the most commonly exploited type of vulnerability, a trend which also was observed in Q1 2022. This is likely due to the range of malicious activities an actor can conduct when exploiting this type of bug. RCE attacks allow an attacker to remotely execute malicious code on a computer and exploitation can result in a complete compromise of a susceptible device, web application, or server.
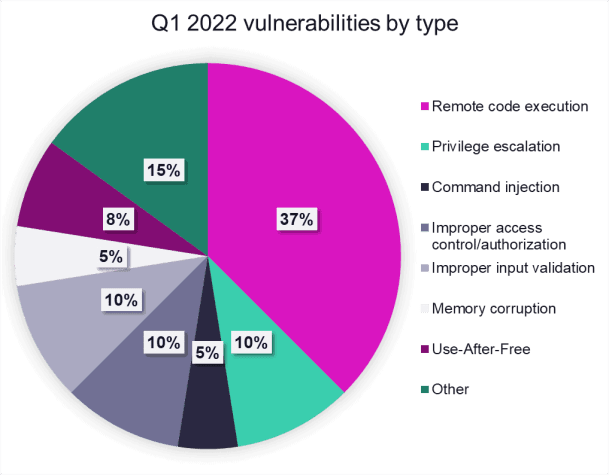
Q1 2022 vulnerabilities by type
Log4Shell hangs in the balance
Initially reported on 10 Dec 2021, the zero-day vulnerability CVE-2021-44228, more commonly known as Log4Shell, continued to present problems in the first quarter of 2022. On 03 Jan 2022, Microsoft stated that threat actors had added exploits for the Log4j vulnerabilities in their attacks and were using them to establish reverse shells, drop remote access tools, and to conduct hands-on keyboard attacks against vulnerable systems.
Furthermore, Microsoft disclosed they had seen some of these attackers eventually deploying ransomware in post-exploitation environments. In fact, Log4Shell was the most discussed vulnerability across a wide range of sources, including tweets, pastes, blogs, webpages, internet relay chats, and Github (see graph below).

Q1 2022 mentions of CVE’s across select open sources
Nation-state threat actors also exploited Log4Shell in Q1 2022. The Chinese state-associated threat group APT41 compromised six US state government networks exploiting the Log4Shell vulnerability, and also targeted insurance and telecommunication companies vulnerable to the flaw.
In March 2022, it was widely reported that a new malware, dubbed “B1txor20”, exploits the Log4Shell vulnerability to compromise new devices, before adding them to its botnet to steal sensitive data, install rootkits, create reverse shells, and act as web traffic proxies.
The season of Spring4Shell
As if we didn’t have enough to worry about with the Log4Shell hangover from the previous quarter, another similar RCE critical vulnerability sprung onto the scene dubbed “Spring4Shell”, a vulnerability in the Java-based Spring Framework that is most commonly exploited using Apache Tomcat. The vulnerability could allow malicious actors to achieve remote code execution in Spring Core applications under non-default circumstances, granting the attackers full control over compromised devices.
Similar to Log4Shell, threat actors were quick to exploit Spring4Shell after its initial disclosure. On 01 Apr 2022, security researchers reported on the first known exploitation of Spring4Shell by threat actors executing the Mirai botnet malware. The US Cybersecurity and Infrastructure Agency (CISA) later warned of active exploitation of Spring4Shell in the wild, and Microsoft confirmed a “low volume of exploit attempts” across the company’s cloud services for Spring Cloud and Spring Core vulnerabilities.
Fortunately, despite the vulnerability’s initial hype and comparisons to Log4Shell, Spring4Shell presents a less formidable threat because it has steeper requirements for exploitation.
Dirty Pipe privilege escalation vulnerability in Linux
Privilege escalation vulnerabilities are security issues that allow users to obtain higher levels of permission and access to systems or applications than their administrators intended. Although these flaws may have taken a short-term backseat to the popular RCE vulnerabilities discussed in the media this quarter, they remained extremely popular among cybercriminals. ReliaQuest found more references to privilege escalation vulnerabilities by cybercriminals than any other type of vulnerability in Q1 2022 (see graph below).

Mentions of references to vulnerabilities from October 2021 – March 2022
One such privilege escalation vulnerability dubbed “Dirty Pipe” made considerable noise in March 2022 upon its discovery by one researcher. Tracked as CVE-2022-0847, Dirty Pipe is a flaw in the Linux kernel that allows an unprivileged process to write to any file it can read, even if it does not have write permissions on this file.
If exploited, it could grant even the least privileged users to obtain root privileges through publicly available exploits – a pretty massive flaw for such a prominent operating system as Linux. Threat actors could utilize Dirty Pipe to conduct lateral movement, execute arbitrary code, or propagate malware and viruses. At the time of writing, Dirty Pipe has been patched for Linux versions 5.16.11, 5.15.25, and 5.10.102, and Android’s version of the Linux kernel.
DPRK takes aim at Google Chrome zero-day vulnerability
First disclosed on 23 Mar 2022, CVE-2022-0609, is a use-after-free (UAF) vulnerability – a vulnerability related to incorrect use of dynamic memory during program operation – in Google Chrome’s animation component. In Q1 2022, the flaw was exploited by two North Korea-based threat groups tracked as “Dream Job” and “AppleJeus” in campaigns targeting US-based organizations in the media, IT, cryptocurrency, and financial-technology (FinTech) industries.
The two threat groups, although tracked as separate entities, made use of the same exploit kit to compromise targeted users in phishing campaigns. The attackers placed links to the exploit kit within hidden iframes, which they embedded on websites they owned as well as some websites they compromised.
This was one of two-zero day vulnerabilities found in Chrome in Q1 2022, the other being CVE-2022-1096, a vulnerability in the V8 JavaScript engine. A patch is available for both zero-days – Google Chrome users only need to update to the browser’s latest versions to avoid falling victim to these vulnerabilities.
Taking a risk-based approach to vulnerability remediation
There will never be a ‘perfect’ method of vulnerability remediation, and if it feels like you’re constantly playing catchup, this feeling is commonplace across many companies. Whatever the resources or headcount available at your disposal, the best way to address vulnerabilities is by taking a risk-based approach; this is a process that reduces vulnerabilities across your attack surface by prioritizing remediation based on the risks they pose to your organization.





