Mergers and acquisitions (M&A)* are expected to grow in 2023 as companies take advantage of a turbulent economy. Cybersecurity M&A should play a key role during the process, from pre-deal due diligence to controlling risk during integration and operation phases.
This blog provides some key lessons that ReliaQuest has learned over the years as we have helped CISOs to add value and control risk throughout the M&A lifecycle.
The Mergers and Acquisitions Deal Cycle
M&A typically has two major phases: pre-deal and post-deal.
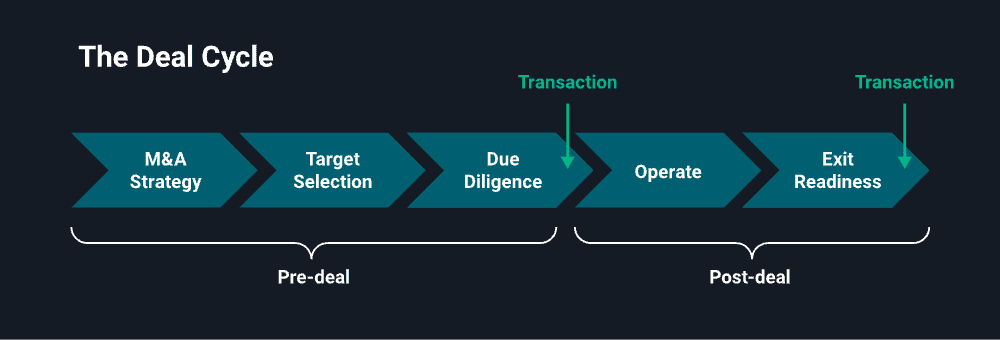
During pre-deal, the CISO or the security team as a whole considers the cybersecurity posture of the target company. They work to identify potential cybersecurity risks, such as unannounced data breaches that might diminish the value of the target or tarnish the acquiring company.
The post-deal stage is when the CISO or security leaders need to consider how they are going to manage risk in the acquired company while controlling costs. Some acquired companies may operate with relative independence from the “mothership” acquiring company, or the separate security operations may be an interim stage as the mothership works to integrate operations more tightly.
And, of course, there is a big focus on rationalizing costs by consolidating and standardizing the cybersecurity technology stacks.
1. Cybersecurity Due Diligence: Evaluating the Security of the Acquisition Target
As the deal progresses into the due diligence phase, the cybersecurity team can provide the answers to critical questions. Has the target suffered an undisclosed data breach or had sensitive credentials leaked to the dark web? What sort of brand risk does the target have? Are there technical weaknesses or vulnerabilities in the acquisition target? The answers to these questions can help you negotiate an optimal deal and prepare for what follows.
2. Integrating Security Operations Post-Merger
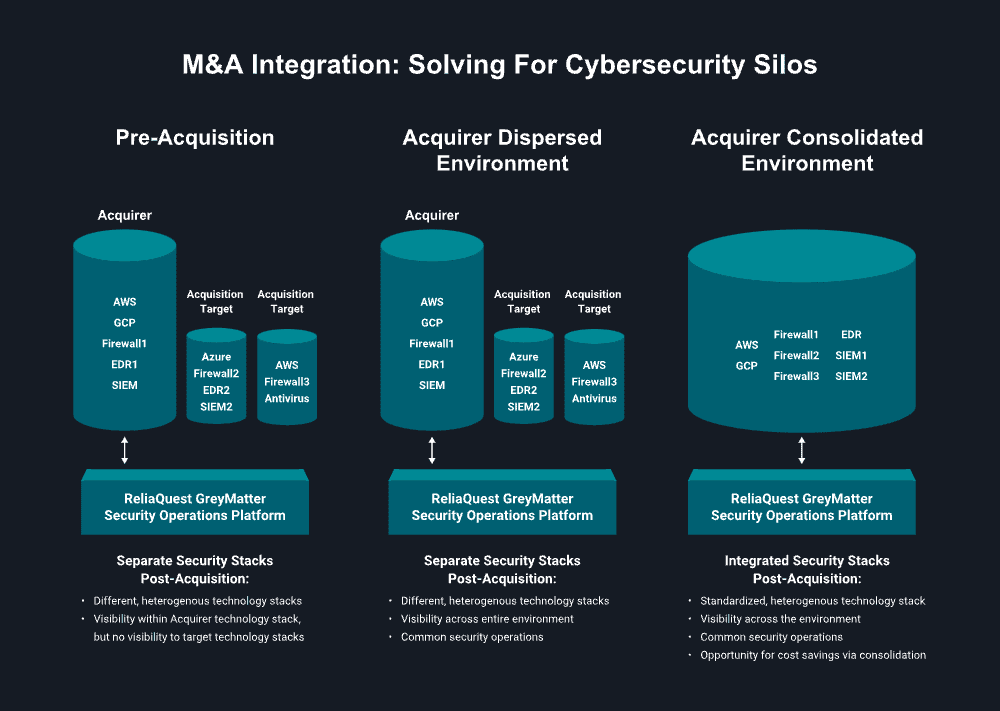
The pre-acquisition stages are fairly consistent, but there are myriad approaches to integrating cybersecurity operations post-acquisition.
For example, the strategy might be to have the acquired company operate separately in perpetuity. Or you might have an interim step following the deal’s close, with the acquired company operating relatively independently until reaching the final goal of a consolidated environment.
Or, if a company’s IT function is a “shared service” across various portfolio companies, the post-deal architecture might look something like middle figure below. In this situation, the mothership maintains visibility across all environments and implements common threat detection logic and endpoint security solutions across the portfolio of businesses, but the acquired business units have some independence.
No matter which operating model your organization decides on, flexibility is key to reaching that final destination. If either the acquiring or the target company has a rigid infrastructure that only supports a single EDR solution or requires all business units to implement a common security stack, they may struggle to integrate quickly and can suffer from security blind spots. Unfortunately, rarely do two companies have the same tool infrastructure, so a merger can result in a hodgepodge of solutions from multiple vendors. Having a that can integrate and use that multi-vendor hodgepodge will ensure better visibility, reduced complexity, and improved risk management.
5 Cybersecurity M&A Considerations
At ReliaQuest, we have years of experience using our GreyMatter security operations platform to power a variety of M&A security models. We’ve seen a few things. That experience has brought to light several best practices for cybersecurity leaders to add value during the M&A process. What follows are major cybersecurity M&A “lessons learned”:
1. Take a deal vs. risk approach
Instead of approaching M&A from exclusively a conventional cybersecurity risk assessment perspective, organizations should take a step back and consider the deal itself. What are the cybersecurity risks that might affect the deal value?
2. Consider digital risk protection during due diligence
Services like ReliaQuest GreyMatter Digital Risk Protection—which scour the open, deep, and dark web—can identify pre-deal risks that might affect deal value or viability.
3. Prepare to mitigate risk post-signing
If you are not part of the deal team, you might want to knock on their door to get visibility to the approaching cybersecurity risks that you might inherit.
4. Have a strategy for post-deal costs and integration
Preparing a strategy for integration and knowing the costs associated with that strategy sets you up for future success. Knowing your integration plan, the level of visibility and type of metrics you’ll need, and any anticipated operational costs will allow you to meet or exceed board expectations.
5. Use a security operations platform to optimize flexibility and visibility
Consolidating the mothership and acquisition target infrastructures does not happen overnight. During the process, you need to maintain visibility across your new, expanded attack surface, but also maintain flexibility to mitigate risk as you combine multi-vendor security stacks in a way that makes sense for your business.
Security Operations Platforms for Cybersecurity M&A
If you need help making cybersecurity possible as your company works through M&A activity, can provide you with the flexibility to embrace M&A acquisitions by delivering visibility, cutting through complexity of heterogenous security stacks, and managing risk and uncertainty so your business can achieve its goals.
* Editor’s note: “M&A” is shorthand that describes a variety of different transactions. Those scenarios include mergers, acquisitions, divestitures, joint ventures, private equity, and managing cybersecurity for a collection of portfolio companies. While the industry talks about “cybersecurity for M&A”, that could be any number of models, from consolidating security stacks to operating and monitoring a collection of different stacks. In the content of this blog, M&A refers to this broad collection of different scenarios.





