This blog examines a newly launched DDoS protection filter mechanism dubbed EndGame advertised last week on the dark web community forum Dread, which required a combined effort from many parts of the dark web to create a solution for an ongoing problem that has been slowly killing off the cybercriminal scene one platform at a time. We’ll look at this new tool-set and its features, the team behind the tool, the impact it could have on the cybercriminal scene, and why DDoS attacks could ultimately become a thing of the past.
Why Is a DDoS Protection Filter Needed?
The dark web is incessantly plagued with DDoS attacks that knock cybercriminal forums and marketplaces offline, whether this be threat actors incentivized by the thought of a significant pay-day through an extortion attempt, rival platforms disrupting their competition, or law enforcement trying to disable the platform.
Despite the best efforts of such platforms’ administration teams to defend against these attacks, they keep on coming. This may be down to the intent of the entity behind the incident: The determination of the attacker may significantly exceed the resolve of the defenders. Or it could be because a DDoS rental service can be purchased for as little as USD 10 per hour, USD 200 per day, or USD 1200 per week. The financial costs of carrying out an attack are not significant enough to outweigh the potential rewards of extorting the victim site’s owners further down the line.
Marketplace and forum administration teams have historically cited vulnerabilities in the Tor network itself as the underlying reason for these attacks’ effectiveness. For example, many have attributed the 2019 demise of Dream Market to an extortion effort following a sustained DDoS attack that was facilitated by a weakness in the Tor network. At the time of the attack, a moderator affiliated with Dream Market complained about this vulnerability on Dread and refused to pay the extortion fee demanded by the threat actor. Other services, including Libertas Market, even attempted to switch from Tor to the alternative anonymity network I2P to mitigate the threat of ongoing DDoS activity. However, due to the limited use of I2P as a fast and reliable platform, this move ultimately resulted in the market shutting down.
Other notable DDoS victims include the dark web marketplaces Empire and Nightmare. Empire is still active today and is regarded as one of the most popular marketplaces available, and Nightmare executed an exit scam in August 2019. Dread itself also fell victim to a DDoS attack in January 2020, but some quick thinking and network analysis by the administrator enabled the service to mitigate the attack and return to normal. However, success stories like this are few and far between.
Speed and availability are two critical factors a user might consider when deciding which dark web service to favor over another. If it proves impossible to connect to a marketplace or forum or the speed of a service is more akin to a snail’s pace, users will become disgruntled and leave the platform without a moment’s hesitation. This ultimately destroys the service’s reputation and credibility. So it’s easy to see why the idea of a DDoS filter protection mechanism would be music to a lot of ears fed up with the current prevalence of DDoS activity in the dark web scene.
What Is the EndGame Tool and Who Is Behind It?
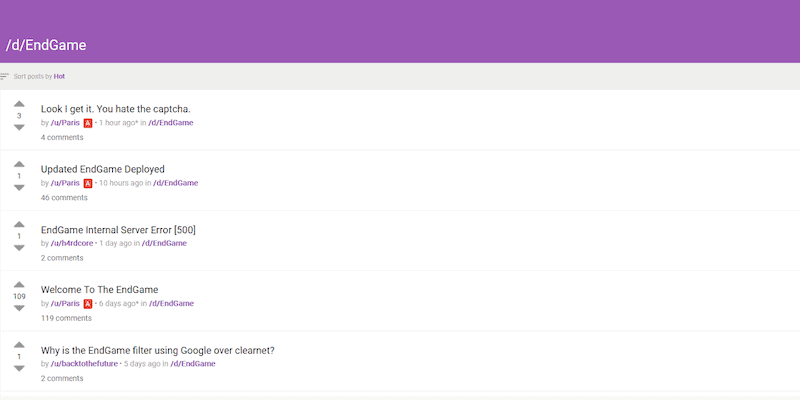
On 26 May 2020, a Dread moderator announced the release of a DDoS protection filter mechanism called “EndGame” that would be free for the community.
In a nutshell, EndGame is a collation of tools designed to prevent DDoS attacks on the front end against both dark web services, and whoever else might be interested. The project appears to have been a long time in the making: Its co-creator mentioned it consists of “thousands of lines of code using 8 open source projects, 6 open source NGINX modules, 6 open source libraries and MONTHS worth of work and testing”.
While projects like this would typically be open source, EndGame’s contents are yet to be publicly released. The Dread moderator said that the tool’s creators didn’t want to delay the mechanism’s launch and so shared the tool freely with the Dread community to gauge opinion. They added that a GitHub project for the mechanism would be created when they “get the time.”
Although EndGame was first revealed on Dread, its launch announcement stated that it was a combined effort, with assistance coming from those affiliated with the dark web marketplaces White House Market, Big Blue Market, and Empire Market.
The Dread post announcing the project highlighted several of the tool-set’s purported features and advantages, including:
“A front system designed to protect the core application servers on an onion service in a safe and private way”
“Locally compiled and locally run (no trusted or middle party)”
“A combination of multiple different technologies working together in harmony”
“FREE FOR ALL TO USE!”
“Fully scripted and easily deploy-able (for mass scaling!) on blank Debian 10 systems”
“Full featured NGINX LUA script to filter packets and provide a captcha directly using the NGINX layer”
“Rate limiting via Tor’s V3 onion service circuit ID system with secondary rate limiting based on a testcookie like system”
“Easy Configuration for both local and remote (over Tor) front systems”
“Easily configurable and change-able to meet an onion service’s needs”
Response to the DDoS on Dread
Initial reactions on Dread to the toolset’s release have been mostly positive, with little negative feedback.
One Dread user did highlight a weakness in the tool, stating, “Publishing a generator means this captcha will be 100% cracked in less than a day.” The user advised the tool’s creators to “switch back to a text based captcha.” They reasoned: “Sure, you might have to deal with 2captcha/Anti-Captcha f*****s paying poor people in 3rd world countries to do the captchas for them, but that quickly becomes costly. Text based captchas, at least with good background static, are much harder to crack with machine learning just because they contain more entropy.”
The Dread moderator welcomed the feedback, recognizing that although the CAPTCHA generator recommended for use with this toolset required some further work, it was only one part of the whole toolset.
Another Dread user opined, “captcha is only a part of EndGame and.” They indicated that EndGame is more than just a CAPTCHA generator, saying “even if [it is] broken it won’t help with ddos but mostly with spam.” They also suggested that EndGame users should customize the tool to their desired specification: “The whole thing is modular so operators can (and should) get creative.”
Potential Impact of the Tool
If EndGame gains traction and suitably impresses users, we may see increasing numbers of dark web marketplaces and forums implementing this protection mechanism. Significant effort is likely to have been spent on compiling this tool-set and its individual components to provide a complete front-end protection service. However, the threat of DDoS attacks and extortions will only persist if there are avenues of weakness that can be exploited. If platforms start introducing protection features that increase both the time and money an adversary must spend to compromise a victim’s service, the threat will likely decrease.
The collaborative effort to find a possible solution to an ongoing problem indicates the community’s intent to stop DDoS attacks against dark web services once and for all. While we cannot tell whether EndGame will eradicate DDoSing activities across the dark web community, a tool-set offering a number of features, customizations, and solutions moves the scene into a much better position than before.