Colonial Pipeline and DarkSide Ransomware
On Friday, May 7, Colonial Pipeline took down parts of their IT infrastructure in the wake of a ransomware attack. The pipeline supplies 45% of the U.S. East Coast’s gas, diesel and jet fuel. The FBI confirmed on Monday that the criminal group responsible is leveraging the DarkSide RaaS (Ransomware-as-a-Service). The DarkSide group which has built the ransomware software and hosts the infrastructure rents out their platform to other groups who conduct the actual infiltration and attacks.
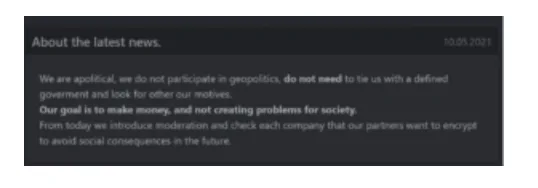
DarkSide is an interesting group as they have a code of conduct which implies, they will not attack hospitals, schools, and government organizations. The group also builds customized executables for each company targeted, so it is unclear if they were aware, they were targeting the pipeline, however they issued a “press release” stating they will vet targets in the future.
Moving forward relying on the benevolence of malware authors is not a sound security strategy and no industry or organization is safe from ransomware. Last month ReliaQuest provided our customers with a threat advisory report regarding ransomware which included an outline of key behaviors to monitor for ransomware. As ransomware is increasingly customized for specific organizations, and the infrastructure constantly changes, relying on IoCs alone can be a challenge and multiple layered preventative and response controls should be deployed.
ReliaQuest’s Threat Management Team continues to monitor the threat posed by DarkSide and other ransomware families and continuously updates our Intel and Detect capabilities within the GreyMatter platform, ensuring our customers have the most up-to-date coverage.
Ransomware Costs More Than the Ransom
The Colonial Pipeline ransomware case reveals that the cost of ransomware goes well beyond just the ransom demanded, even as these ransom demands increase. The cost to business continuity can often be difficult to quantify, until it actually happens to an organization. Some of the other costs of a ransomware outbreak that businesses often fail to consider include:
Insurance – Some insurance companies may pay the ransom, but there have been some interesting conversations happening about this no longer being covered in the future. Although some costs and even the ransom may be covered in some cases, there is still a deductible that needs to be paid. Many insurance companies may also have a clause in their policies referred to as “Failed to Maintain” which deals with negligence on the company’s part if they fail to maintain minimum/adequate security standards.
Incident Response – Ransomware didn’t just appear on your network, the organization needs to figure out the root cause, what other things the attackers did and what data was accessed, exfiltrated. If you don’t have your incident response sorted out, it will happen again. A third-party may need to be called in if the right talent is not on the team, often companies have these types of services on retainer.
Legal – You will need to navigate the minefield of reporting obligations, ensure communications are privileged so opposing counsel can’t seem them if you are sued. Legal will also need to advise the company if paying a ransom is even legal. Many ransomware groups are not just encrypting data, but also exfiltrating it and possibly selling or dumping it so it is public. Legal will need to be involved with the incident response process to determine what compliance risks the compromise poses.
Crisis Communications – How to notify customers that may be affected by business continuity or if their data has been compromised. A crisis communications or specialty firm may be called in to help.
IT Support – Recovery from a ransomware attack is a 24/7 job and your IT team will burn out, organizations often need to bring in outside help to manage the incident response, forensics as well as remediation to ensure the infection is completely removed from the environment.
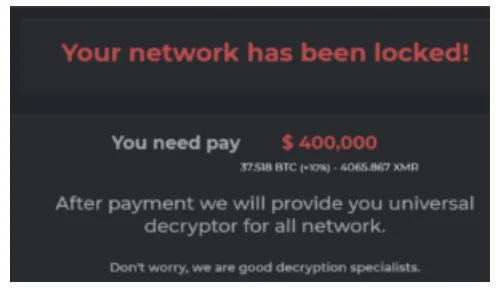
Ransom – A determination must be made by the organization whether they will pay the ransom or not, if they don’t pay the ransom what will be the impact to the business?
Ransomware Negotiator – There are organizations who help negotiate the ransom and more importantly try to ensure the compromised data is deleted, however there are no guarantees.
Other – Additional costs may include, fines, hardware, software recovery costs, loss of productivity, lawsuits, loss of customers and ongoing monitoring.
As we have seen with the Colonial Pipeline, the effects of ransomware can be disastrous. We have seen business continuity affected in the past, but bringing down a pipeline that delivers almost half the gas, jet fuel and diesel to the Eastern United States has raised the stakes even higher. The cost of ransomware is not just the cost of the ransom itself, but also the cost associated with bringing critical systems down whether it’s a pipeline, hospital, key communication infrastructure, or critical business systems. Some of these costs are well beyond dollars and can have a significant impact on people’s lives. Organizations need to take the ransomware threat seriously and deploy appropriate preventative and response controls to properly mitigate the threat that goes beyond the perimeter.




