Application programming interface (API) keys are a precious commodity in the world of cybersecurity. A vital component of modern developmental processes, they allow the authentication and authorization of a specific user, developer, or program to an API. API keys have distinct advantages, like verifying user identify identity and permissions when making certain requests to an API—which can reduce the risk of hackers pretending to be end users of an application.
But API keys aren’t foolproof. If one is stolen, it may be used indefinitely―because it has no expiration―unless the project owner revokes or regenerates the key. Read on for our insights on API keys, and how you can protect them.
The Tremendous Value of the API
API keys can be thought of as passwords that allow computer programs to talk to each other. They’re often long strings of characters or numbers (e.g., AIzaSyDaGmWKa4JsXZ-HjGw7ISLn_3namBGewQe) that allow access to data, resources, or program-to-program functionality. For example, an API key might let a user authenticate a computer or query a database looking for specific information; ReliaQuest research revealed that 40% of exposed API keys have been used for database stores.
A cloud API enables applications to communicate with each other and exchange information in the cloud, interacting with programs programmatically and connecting multiple clouds or linking cloud apps to on-premises apps. This type of API uses keys, too, which can bring severe consequences to the cloud environment if an attacker gets hold of a key.
Security controls to identify exposed API keys have developed a lot recently. Still, exposures often manage to slip through multiple layers of controls, leaving the door to networks open. To identify exposed API keys, a threat actor often begins with reconnaissance of organizational resources that are publicly available for anyone to access. They might scrape public repositories or inspect web apps that use APIs.
After they find an exposed access key, the threat actor often uses it first: performing discovery commands to enumerate instances and roles associated with them, as a precursor to identifying sensitive information to steal or delete. Typically, but depending on the access the key offers, the threat actor then attempts to maintain persistence and escalate privileges. They do this by creating additional accounts, keys, or roles that enable them to access resources through more conventional methods if the API key is revoked.
With a stronger foothold in the environment, it is not uncommon for a threat actor to also open ingress traffic on Port 22 (SSH/SFTP) for security groups tied to the exposed API key. This creates a secure channel for the attacker to send data through. These attacks tend to end with data exfiltration: The threat actor quickly identifies and moves the data out of the network.
Stolen Keys to the API Kingdom
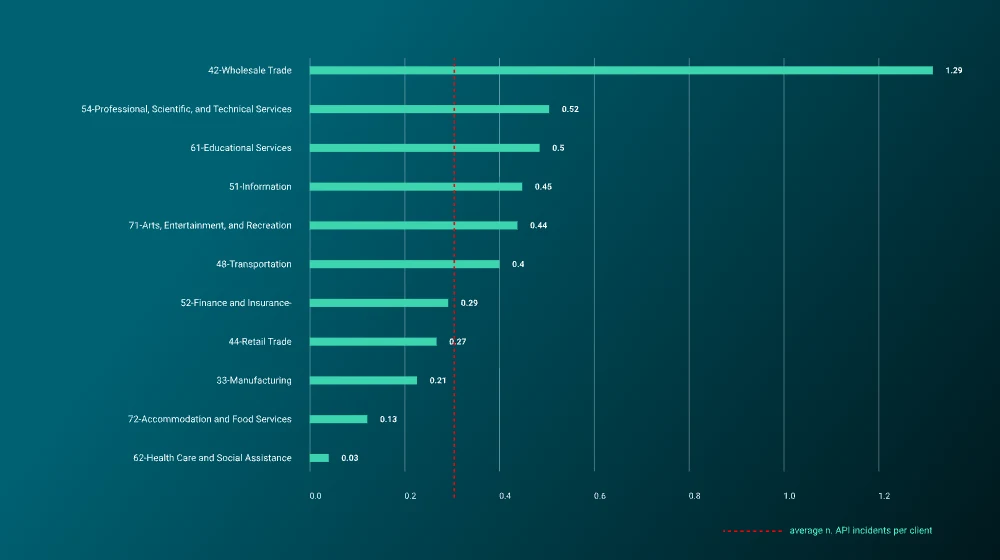
What does our data on API keys show? Well, from our analysis of alerts to ReliaQuest customers, we can see that the sector most affected by API-related incidents was wholesale trade, followed by professional, technical, and scientific services, then education. Figure 9 shows the average number of such incidents that affected customers, by sector, during the reporting period. The red bar shows the average number of API incidents across all sectors; so if your sector is right of the bar, you’re doing worse than the majority of other sectors.
So what does this mean? API keys are an important piece of modern networking and must be properly secured to keep your environment secure. In many instances, the risk associated with exposed keys can be prevented by not hard-coding API keys into application data. Additionally, monitoring API usage and looking for anomalous activity can identify security faults.
Also, rotate your API keys. Remember: API keys can be seen as passwords and should be treated as such. There is no one solution to eliminate the risk of exposed API keys, but implementing a layered defense will be the best method of minimizing the risk of an API-related incident.
How ReliaQuest Can Help
ReliaQuest GreyMatter enables our customers to continuously identify and mitigate risks arising from the exposure of sensitive information on GitHub, on other code repositories, and elsewhere across the open, deep, and dark web. Alongside API key exposures, port exposures, fake domains, and credential exposures, all the intelligence is delivered to you via a timely alerting system, which also tracks any demonstrable change to the risk over time.
Armed with this intel, our customers can take proactive action before any breaches are exploited by malicious actors. GreyMatter customers are also protected through a robust detection library that enhances the visibility of cloud-based threats.
How to Protect Yourself
Considering the risk attached to a breach, organizations must sufficiently ensure their API keys are secure and handled safely:





